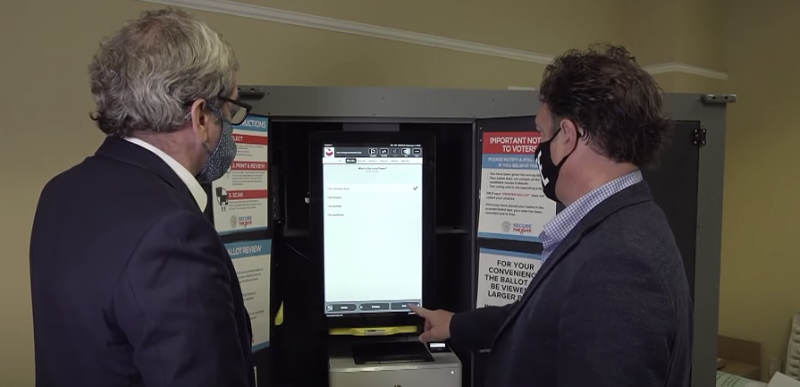
PBS Newshour did a piece on the Dominion voting systems in Georgia before the election and what they found was troubling to several experts:
GEORGIA.🗳️
One week before the election.
PBS (Public Broadcasting Systems) does a deep dive on Georgia's use of Dominion Voting Systems machines.
What they found was troubling.🔽 pic.twitter.com/RzwI3spw4Z
— Kyle Becker (@kylenabecker) November 13, 2020
PBS Newshour had a ‘white hat hacker’ named Harri Hursti inspect the system and he said “they have set up a complicated system which is centralized; it doesn’t seem to have any safeguards.”
They described the system as having a lot of moving parts, saying “it’s an assortment of laptops, iPads, magnetic cards, touch screens, printers and scanners.”
PBS says the devices replaced touchscreens in 2019 which didn’t created a paper ballot, but one of the women responsible for bringing about this change isn’t terribly happy with the new system either. And election experts have found several troubling problems with the new system, especially the Q.R. codes it creates for tabulation:
Alex Halderman looked closely at the Q.R. codes where the votes are encoded for the scanner. “By analyzing the structure of the Q.R. codes, I have been able to learn that there’s nothing that stops an attacker from just duplicating one, and the duplicate would count the same as the original barcode.”
And in late September, another concern came to light. During testing, election workers found half the names of the 21 candidates for Senate intermittently disappeared from screens during the review phase. Dominion sent out a last-minute software patch.
Halderman caution: “I’m worried that the Georgia system is the technical equivalent to the 737 MAX. They have just made a last-minute software change that might well have unintended consequences and cause even more severe problems on Election Day.”
Hirsti expressed concern that the system was being rushed out with the proper testing:
You never want to rush something which is mission-critical, and this is mission-critical, into production without proper time for testing.
That’s really one of the ways bad actors are finding the vulnerabilities to exploit is looking for honest vulnerabilities and finding out if they can be weaponized, if they can be exploited.
The actual segment goes on for 7 minutes and you can watch it below: